| Name | Last Modified | Size | Type |
|---|---|---|---|
| bin/ | 2017-Dec-12 16:28:30 | -- | Directory |
| etc/ | 2017-Dec-12 16:19:30 | -- | Directory |
| testssl-robot.zip | 2017-Dec-12 15:30:02 | 160.97KB | ZIP Compressed Archive |
| testssl-robot.zip.asc | 2017-Dec-12 16:02:49 | 811.00B | ASC File |
| testssl.sh | 2017-Dec-12 16:02:03 | 762.84KB | SH File |
| testssl.sh.asc | 2017-Dec-12 16:02:57 | 811.00B | ASC File |
 .
.
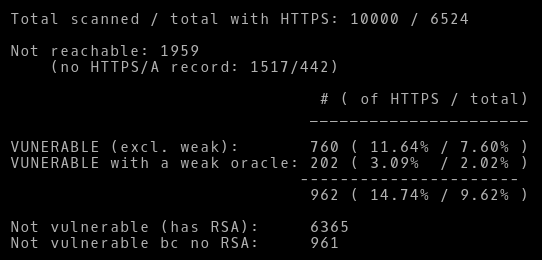
Dec 14, 2017: I scanned the Alexa Top 10k on the 12th and 13, the result is rather disillusioning: Almost 15% of the Internet currently is broken! At least if take the number of hosts using HTTPS as a basis. If you subtract the hosts showing a weak oracle the percentage is still around 11.5%. Amongst them were lots of high profile hosts like ebay.com (and other TLDs), hp.com, citrix.com, cisco.com, apple.com, itunes.com, fidelity.com, aliexpress.com, walmart.com, verizonwireless.com – to name a few (see my twitter feed). I am probably going to publish the screenhots later here too.
Also banks I spotted quite a few: of 65 hosts in the top 10k having the pattern "bank" in their hostname 13 (20%) were vulnerable. "edu" was worse – which is given the hardware basis of this bug – quite surprising: 31 (21.6%) of 143 hostnames appear vulnerable.
If you did the math and were wondering: Adding all vulnerable and non-vulnerable hosts is more than the number of total hosts with HTTPS. This is due to the fact that hostnames resolving to more than one IPs address gave different results for different IP addresses (vulnerable + not vulnerable or not reachable). For the sake of simplicity those hosts I counted more than once, mathematically more exact would have been to use fractions of a hostname then.
bash is a prerequisite – otherwise there would
be no sockets.
./testssl.sh --robot <URI> or
./testssl.sh -BB <URI>
host | host:port | URL | URL:port
./testssl.sh --robot --starttls <URI>.
Examples (old, they do not work anymore):
userid@somehost:~ % ./testssl.sh --robot cisco.com
##########################################################
testssl.sh 2.9dev from https://testssl.sh/dev/
(7e62dc3 2017-12-07 09:59:58 -- )
This program is free software. Distribution and
modification under GPLv2 permitted.
USAGE w/o ANY WARRANTY. USE IT AT YOUR OWN RISK!
Please file bugs @ https://testssl.sh/bugs/
###########################################################
Using "OpenSSL 1.0.2-chacha (1.0.2i-dev)" [~183 ciphers]
on mr_robot:./bin/openssl.Linux.x86_64
(built: "Jun 22 19:32:29 2016", platform: "linux-x86_64")
Start 2017-12-12 00:08:06 -->> 72.163.4.161:443 (cisco.com) <<--
further IP addresses: 2001:420:1101:1::a
rDNS (72.163.4.161): www1.cisco.com.
Service detected: HTTP
Testing for Return of Bleichenbacher's Oracle Threat (ROBOT) vulnerability
ROBOT VULNERABLE (NOT ok)
Done 2017-12-12 00:08:19 [ 15s] -->>.163.4.161:443 (cisco.com) <<--
userid@somehost:~ % ./testssl.sh -BB --starttls pop3 px.hboeck.de:110
###########################################################
testssl.sh 2.9dev from https://testssl.sh/dev/
(7e62dc3 2017-12-07 09:59:58 -- )
This program is free software. Distribution and
modification under GPLv2 permitted.
USAGE w/o ANY WARRANTY. USE IT AT YOUR OWN RISK!
Please file bugs @ https://testssl.sh/bugs/
###########################################################
Using "OpenSSL 1.0.2-chacha (1.0.2i-dev)" [~183 ciphers]
on mr_robot:./bin/openssl.Linux.x86_64
(built: "Jun 22 19:32:29 2016", platform: "linux-x86_64")
Start 2017-12-12 01:21:24 -->>.202.78.80:110 (px.hboeck.de) <<--
rDNS (149.202.78.80): ns3608653.ip-149-202-78.eu.
Service set: STARTTLS via POP3
Testing for Return of Bleichenbacher's Oracle Threat (ROBOT) vulnerability
ROBOT VULNERABLE (NOT ok)
Done 2017-12-12 01:21:33 [ 11s] -->> 149.202.78.80:110 (px.hboeck.de) <<--
userid@somehost:~ %
 Please note that this is a snapshot of the code from December 2017..
Please note that this is a snapshot of the code from December 2017..